24/7 – 365 Protection From Cyber Attacks
Information Security Policies
All businesses should maintain up to date Information Security (InfoSec) policies in order to help protect your company from threats inside and out. These policies can be tailored for your business to comply with any regulatory or compliance standards you are required to meet while laying out technology guidelines for your staff to follow to help prevent an issue before it can happen. CPU can work with you to create an InfoSec policy that will increase your security posture and help keep your business secure.
Onsite Staff Security Training
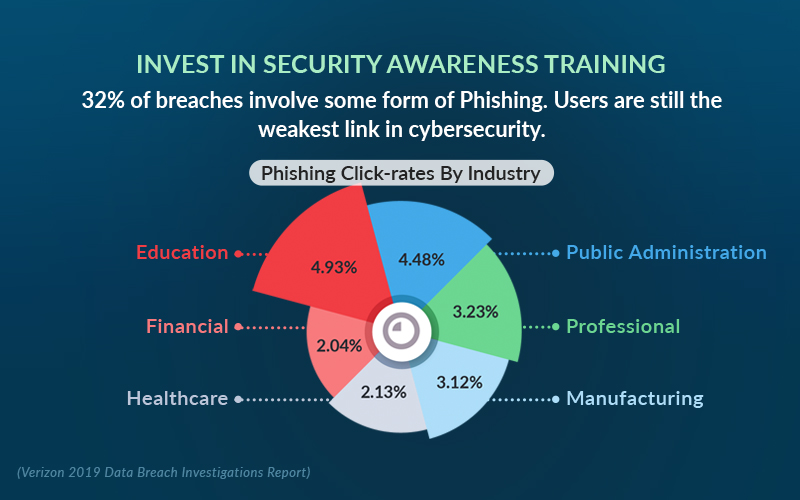
CPU also offers comprehensive security awareness training on a variety of Cybersecurity topics to train employees. These trainings can occur at your business, through webinar, or pre-recorded sessions whichever method is preferred by your business. Employees are the front line of your business and proper training can be the difference between a bad actor getting access to privileged information or not. 35% of breaches were directly caused by employees based on the Verizon 2020 Breach Report. This number shows that users are still the weakest link in cybersecurity and we have to put the extra effort in to shore up that weakness.
Compliancy
As part of our commitment to your businesses security posture we offer comprehensive packages to help get your company ready or compliant with any current or upcoming compliancy requirements. Currently we have a focus on HIPAA, PCI, and SOC 1 & 2 as well as the newer CMMC standard. We can tailor policies to your individual compliance requirements as well as engineer your companies’ network to follow compliancy requirements.
Cybersecurity & Compliance
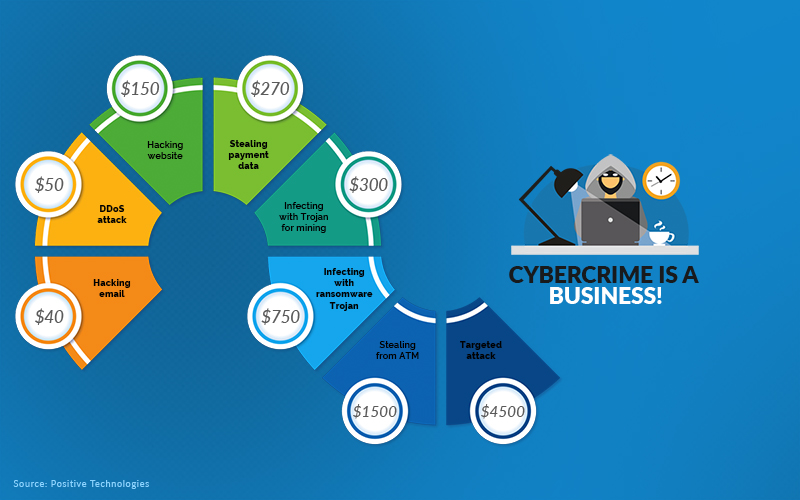
In today’s cyber landscape there is no such thing as having too much protection. Many small to medium sized businesses have no cybersecurity technology or policies in place to protect themselves despite the rise in cybercrime over the past 5 years. Criminals have been adapting their actions and are using more sophisticated methods to look for easy targets with the quickest path to their victims. While this has been happening, most businesses have not made any changes to keep up with these growing threats.
Dark Web
With the crackdown of cybercriminals on the internet they have turned to the darker side of the web. This area called the “Dark Web” is actually a part of the internet that we all know that is uncategorized by our favorite search engines. The only way to access this part of the internet is through a specialized browser which makes it the perfect place for cybercriminals to hangout. This is also where the largest cybercriminal markets and websites are based out of. With our tools CPU is able to scan the Dark Web for stolen or compromised accounts from you or your business. This allows us to proactively protect you from data breaches that may occur without you being aware of it.
Bullphish and Security Training
Over the past few years, we have seen a huge increase in phishing attempts. Phishing is when a bad actor sends an email claiming to be someone else such as Microsoft in order to gain your trust and get you to disclose privileged information or send money. CPU offers a new program called Bullphish where we will create and send phishing emails to your staff to gauge how they will react to a legit email threat. Once that has completed, we can send out automated trainings to specific employees.
Business Risk Assessment and Network Audit
CPU offers network security risk assessments as part of an ongoing monitoring agreement or for one off assessments. Risk assessments are in important part of protecting your business and data. IBM Security estimates that companies, on average, take about 197 days to detect a breach and 69 days to contain it. With regular risk assessments and network audits you can reduce those numbers significantly by taking a proactive approach instead of waiting until it is too late at which point your business could be shut down while you contain the issue. The average requested ransom after a small business breach is $4,300. This goes up to almost $4 million for larger businesses. Without risk assessments, you have no other way of analyzing risks and vulnerabilities in your networks and applications.
Your Business Could Be At Risk!
Should Your Business Be Afraid of the Dark Web?
Hackers and cybercriminals launch attacks every 39 seconds, which is an average of 2,244 times per day, with more than 8 Billion records confirmed to be compromised in the last year alone.
Your information provides a very lucrative business opportunity for cybercriminals. Hackers and scammers are smart and efficient. With just a few key personal details and basic technological skills, these criminals could potentially gain access to some of your most important accounts.
Find out if your business is at risk from cyber attacks. Register for CPU Managed IT Services FREE Dark Web Scan. Keep critical data safe!
Call CPU Managed IT Solutions today at 252-752-3458 or write us with your questions or concerns.